The leak of the LockBit 3.0 ransomware builder last year has led to threat actors abusing the tool to spawn new variants.
Russian cybersecurity company Kaspersky said it detected a ransomware intrusion that deployed a version of LockBit but with a markedly different ransom demand procedure.
"The attacker behind this incident decided to use a different ransom note with a headline related to a previously unknown group, called NATIONAL HAZARD AGENCY," security researchers Eduardo Ovalle and Francesco Figurelli said.
The revamped ransom note directly specified the amount to be paid to obtain the decryption keys, and directed communications to a Tox service and email, unlike the LockBit group, which doesn't mention the amount and uses its own communication and negotiation platform.
NATIONAL HAZARD AGENCY is far from the only cybercrime gang to use the leaked LockBit 3.0 builder. Some of the other threat actors known to leverage it include Bl00dy and Buhti.
Kaspersky noted it detected a total of 396 distinct LockBit samples in its telemetry, of which 312 artifacts were created using the leaked builders. As many as 77 samples make no reference to "LockBit" in the ransom note.
"Many of the detected parameters correspond to the default configuration of the builder, only some contain minor changes," the researchers said. "This indicates the samples were likely developed for urgent needs or possibly by lazy actors."
The disclosure comes as Netenrich delved into a ransomware strain called ADHUBLLKA that has rebranded several times since 2019 (BIT, LOLKEK, OBZ, U2K, and TZW), while targeting individuals and small businesses in exchange for meager payouts in the range of $800 to $1,600 from each victim.
Although each of these iterations come with slight modifications to encryption schemes, ransom notes, and communication methods, a closer inspection has tied them all back to ADHUBLLKA owing to source code and infrastructure similarities.
"When a ransomware is successful out in the wild, it is common to see cybercriminals use the same ransomware samples — slightly tweaking their codebase — to pilot other projects," security researcher Rakesh Krishnan said.
"For example, they may change the encryption scheme, ransom notes, or command-and-control (C2) communication channels and then rebrand themselves as a 'new' ransomware."
Ransomware remains an actively evolving ecosystem, witnessing frequent shifts in tactics and targeting to increasingly focus on Linux environments using families such as Trigona, Monti, and Akira, the latter of which shares links to Conti-affiliated threat actors.
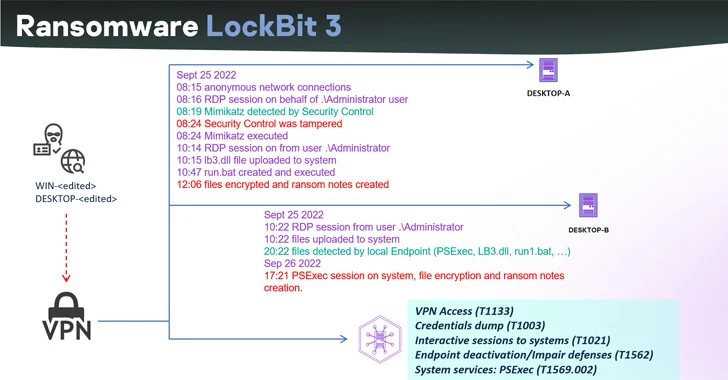
Akira has also been linked to attacks weaponizing Cisco VPN products as an attack vector to gain unauthorized access to enterprise networks. Cisco has since acknowledged that the threat actors are targeting Cisco VPNs that are not configured for multi-factor authentication.
"The attackers often focus on the absence of or known vulnerabilities in multi-factor authentication (MFA) and known vulnerabilities in VPN software," the networking equipment major said.
"Once the attackers have obtained a foothold into a target network, they try to extract credentials through LSASS (Local Security Authority Subsystem Service) dumps to facilitate further movement within the network and elevate privileges if needed."
The development also comes amid a record surge in ransomware attacks, with the Cl0p ransomware group having breached 1,000 known organizations by exploiting flaws in MOVEit Transfer app to gain initial access and encrypt targeted networks.
U.S.-based entities account for 83.9% of the corporate victims, followed by Germany (3.6%), Canada (2.6%), and the U.K. (2.1%). More than 60 million individuals are said to have been impacted by the mass-exploitation campaign that began in May 2023.
However, the blast radius of the supply chain ransomware attack is likely to be much higher. Estimates show that the threat actors are expected to net illicit profits in the range of $75 million to $100 million from their endeavors.
"While the MOVEit campaign may end up impacting over 1,000 companies directly, and an order of magnitude more indirectly, a very very small percentage of victims bothered trying to negotiate, let alone contemplated paying," Coveware said.
"Those that did pay, paid substantially more than prior CloP campaigns, and several times more than the global Average Ransom Amount of $740,144 (+126% from Q1 2023)."
What's more, according to Sophos 2023 Active Adversary Report, the median dwell time for ransomware incidents dropped from nine days in 2022 to five days in the first half of 2023, indicating that "ransomware gangs are moving faster than ever."
In contrast, the median dwell time for non-ransomware incidents increased from 11 to 13 days. The maximum dwell time observed during the time period was 112 days.
"In 81% of ransomware attacks, the final payload was launched outside of traditional working hours, and for those that were deployed during business hours, only five happened on a weekday," the cybersecurity company said. "Nearly half (43%) of ransomware attacks were detected on either Friday or Saturday."