Mozi, a peer-to-peer (P2P) botnet known to target IoT devices, has gained new capabilities that allow it to achieve persistence on network gateways manufactured by Netgear, Huawei, and ZTE, according to latest findings.
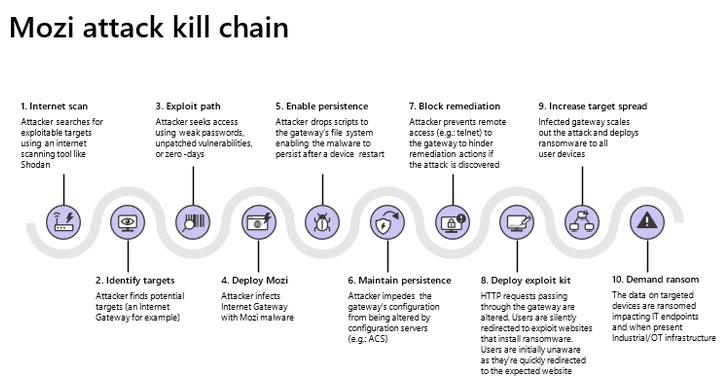
"Network gateways are a particularly juicy target for adversaries because they are ideal as initial access points to corporate networks," researchers at Microsoft Security Threat Intelligence Center and Section 52 at Azure Defender for IoT said in a technical write-up. "By infecting routers, they can perform man-in-the-middle (MITM) attacks—via HTTP hijacking and DNS spoofing—to compromise endpoints and deploy ransomware or cause safety incidents in OT facilities."
First documented by Netlab 360 in December 2019, Mozi has a history of infecting routers and digital video recorders in order to assemble them into an IoT botnet, which could be abused for launching distributed denial-of-service (DDoS) attacks, data exfiltration, and payload execution. The botnet is evolved from the source code of several known malware families such as Gafgyt, Mirai, and IoT Reaper.
Mozi spreads via the use of weak and default remote access passwords as well as through unpatched vulnerabilities, with the IoT malware communicating using a BitTorrent-like Distributed Hash Table (DHT) to record the contact information for other nodes in the botnet, the same mechanism used by file-sharing P2P clients. The compromised devices listen for commands from controller nodes and also attempt to infect other vulnerable targets.
An IBM X-Force analysis published in September 2020 noted that Mozi accounted for nearly 90% of the observed IoT network traffic from October 2019 through June 2020, indicating that threat actors are increasingly taking advantage of the expanding attack surface offered by IoT devices. In a separate investigation released last month, Elastic Security Intelligence and Analytics Team found that at least 24 countries have been targeted to date, with Bulgaria and India leading the pack.
Now fresh research from Microsoft's IoT security team has discovered that the malware "takes specific actions to increase its chances of survival upon reboot or any other attempt by other malware or responders to interfere with its operation," including achieving persistence on targeted devices and blocking TCP ports (23, 2323, 7547, 35000, 50023, and 58000) that are used to gain remote access to the gateway.
What's more, Mozi has been upgraded to support new commands that enable the malware to hijack HTTP sessions and carry out DNS spoofing so as to redirect traffic to an attacker-controlled domain.
Businesses and users using Netgear, Huawei, and ZTE routers are recommended to secure the devices using strong passwords and update the devices to the latest firmware. "Doing so will reduce the attack surfaces leveraged by the botnet and prevent attackers from getting into a position where they can use the newly discovered persistence and other exploit techniques," Microsoft said.