Severe security flaws uncovered in popular Visual Studio Code extensions could enable attackers to compromise local machines as well as build and deployment systems through a developer's integrated development environment (IDE).
The vulnerable extensions could be exploited to run arbitrary code on a developer's system remotely, in what could ultimately pave the way for supply chain attacks.
Some of the extensions in question are "LaTeX Workshop," "Rainbow Fart," "Open in Default Browser," and "Instant Markdown," all of which have cumulatively racked up about two million installations between them.
"Developer machines usually hold significant credentials, allowing them (directly or indirectly) to interact with many parts of the product," researchers from open-source security platform Snyk said in a deep-dive published on May 26. "Leaking a developer's private key can allow a malicious stakeholder to clone important parts of the code base or even connect to production servers."
VS Code extensions, like browser add-ons, allow developers to augment Microsoft's Visual Studio Code source-code editor with additional features like programming languages and debuggers relevant to their development workflows. VS Code is used by 14 million active users, making it a huge attack surface.
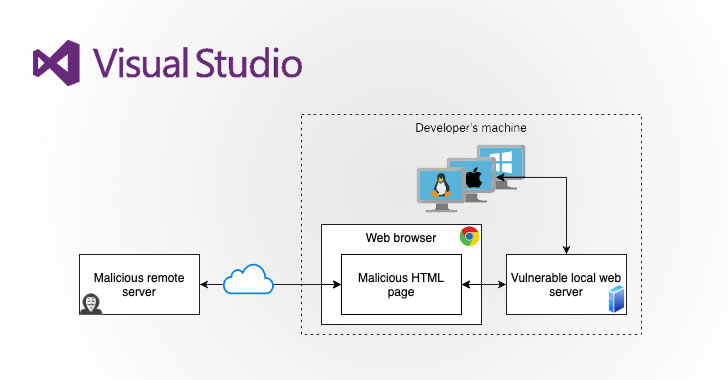
The attack scenarios devised by Snyk bank on the possibility that the installed extensions could be abused as a vector for supply chain attacks by exploiting weaknesses in the plugins to break into a developer system effectively. To that effect, the researchers examined VS Code extensions that had vulnerable implementations of local web servers.
In one case highlighted by Snyk researchers, a path traversal vulnerability identified in Instant Markdown could be leveraged by a nefarious actor with access to the local web server (aka localhost) to retrieve any file hosted on the machine by simply tricking a developer into clicking a malicious URL.
As a proof-of-concept (PoC) demonstration, the researchers showed it was possible to exploit this flaw to steal SSH keys from a developer who is running VS Code and has Instant Markdown or Open in Default Browser installed in the IDE. LaTeX Workshop, on the other hand, was found susceptible to a command injection vulnerability due to unsanitized input that could be exploited to run malicious payloads.
Lastly, an extension named Rainbow Fart was ascertained to have a zip slip vulnerability, which allows an adversary to overwrite arbitrary files on a victim's machine and gain remote code execution. In an attack formulated by the researchers, a specially-crafted ZIP file was sent over an "import-voice-package" endpoint used by the plugin and written to a location that's outside of the working directory of the extension.
"This attack could be used to overwrite files like '.bashrc' and gain remote code execution eventually," the researchers noted.
Although the flaws in the extensions have since been addressed, the findings are important in light of a series of security incidents that show how developers have emerged as a lucrative attack target, what with threat actors unleashing a variety of malware to compromise development tools and environments for other campaigns.
"What has been clear for third-party dependencies is also now clear for IDE plugins — they introduce an inherent risk to an application," Snyk researchers Raul Onitza-Klugman and Kirill Efimov said. "They're potentially dangerous both because of their custom written code pieces and the dependencies they are built upon. What has been shown here for VS Code might be applicable to other IDEs as well, meaning that blindly installing extensions or plugins is not safe (it never has been)."