Cybersecurity researcher Paul Litvak today disclosed an unpatched vulnerability in Microsoft Azure Functions that could be used by an attacker to escalate privileges and escape the Docker container used for hosting them.
The findings come as part of Intezer Lab's investigations into the Azure compute infrastructure.
Following disclosure to Microsoft, the Windows maker is said to have "determined that the vulnerability has no security impact on Function users, since the host itself is still protected by another defense boundary against the elevated position we reached in the container host."
Azure Functions, analogous to Amazon AWS Lambda, is a serverless solution that allows users to run event-triggered code without having to provision or manage infrastructure explicitly while simultaneously making it possible to scale and allocate compute and resources based on demand.
By incorporating Docker into the mix, it makes it possible for developers to easily deploy and run Azure Functions either in the cloud or on-premises.
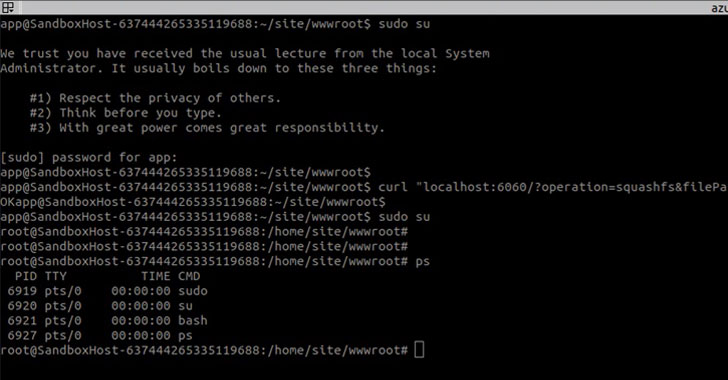
Since the trigger code is an event (e.g., an HTTP request) that is configured to call an Azure Function, the researchers first created an HTTP trigger to gain a foothold over the Function container, using it to find sockets belonging to processes with "root" privileges.
From there, one such privileged process associated with a "Mesh" binary was identified to contain a flaw that could be exploited to grant the "app" user that runs the above Function root permissions.
While the Mesh binary in itself had little to no documentation to explain its purpose, Intezer researchers found references to it in a public Docker image, which they used to reverse engineer and achieve privilege escalation.
In the final step, the extended privileges assigned to the container (using the "--privileged" flag) were abused to escape the Docker container and run an arbitrary command on the host.
Intezer has also released a proof-of-concept (PoC) exploit code on GitHub to probe the Docker host environment.
"Instances like this underscore that vulnerabilities are sometimes out of the cloud user's control," Intezer Labs researchers said. "Attackers can find a way inside through vulnerable third-party software.
"It's critical that you have protection measures in place to detect and terminate when the attacker executes unauthorized code in your production environment. This Zero Trust mentality is even echoed by Microsoft."