Hackers, Government Agencies and sophisticated malware, are collecting every piece of Digital data that we transmit through our Computers, Smartphones or Internet-enabled Gadgets.
No matter how secure you think you might be, something malicious can always happen. Because, "With the right tools and Talent, a Computer is an open book."
Many people ask, How to stay safe and secure online? And, Answer is...
...Knowledge of Cyber threats, little Smartness and a Secure Operating System.
Which Operating System is the Most Secure?
Nearly every Operating System is designed with Security as a requirement, but believe me… there can't be a truly Secure Operating System.
If you are Interested in Security and Hacking, you have probably already heard of various security-focused Operating Systems like Tails, Whonix and Kali Linux.
All these operating systems, including Windows, Linux, BSD, even OSX, are all based on a Monolithic Kernels, and it requires just one successful Kernel Exploit to hack the whole system.
So, a reasonably secure operating system is one that keeps all crucial elements and activities isolated from each other.
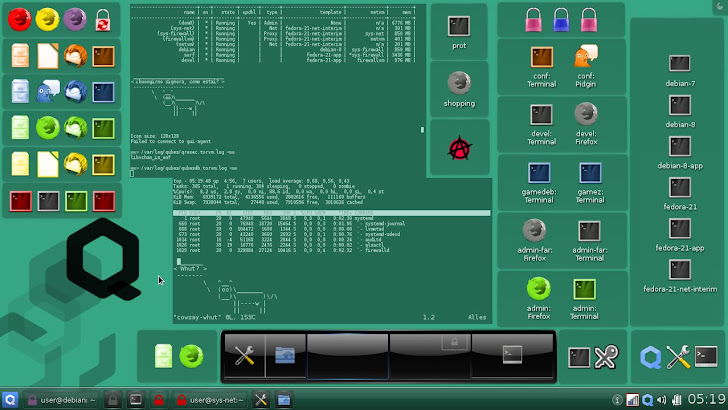
Introducing… Qubes OS, "Security by Isolation."
Qubes OS is a Linux based security-oriented and open-source operating system for personal computers, which runs everything inside the virtual machines.
Its visualization mechanism follows ‘Security by Isolation’ (Software Compartmentalization) principle to secure the systems, i.e. enabling the Principle of least privileges.
So, If you are a victim of a malicious cyber attack, doesn't let an attacker take over your entire computer.
Last week, the team at Invisible Things Project has announced the official release of Qubes 3.0 (Version 3), which is now based on Hypervisor Abstraction Layer (HAL), Xen 4.4 virtualization technology and supports Debian Linux.
Qubes is often misunderstood as a Linux distribution, but instead it can be called as Xen distribution.
Xen is a Native or Bare-Metal Hypervisor that uses a microkernel framework and offer services that allow multiple operating systems to execute on the same computer hardware simultaneously.
A Hypervisor is a computer software, firmware or hardware that allows multiple operating systems to share a single hardware host, where:
Each operating system appears to have the host's processor, memory, and other resources all to itself.
A Hypervisor is of two types, Native/Bare Metal and Hosted Hypervisor; with one running directly on the system hardware and hosting Guest OS and other runs within a Host OS and Hosts Guest OS inside it respectively.
The native/bare metal hypervisor is considered as the Pure Hypervisor as it promises security compartmentalization, reliability and higher security.
Similarly, Xen Hypervisor handles memory management and CPU scheduling of all virtual machines ("domains"), and for launching the most privileged domain ("dom0").
‘dom0’ i.e. Domain Zero, is the control domain of the Xen Hypervisor that has direct access to hardware.
Like Xen, Qubes works in a similar manner by:
- Enabling execution of each separate component in its window environment on the same screen.
- Also, you can view and use each active "window" much like how Linux allows you to open many windows on one desktop screen.
By using Xen Hypervisor, Qubes has tightened the security of a system, as for an attacker, he must be capable of destructing the hypervisor itself in order to compromise the entire system, which is hard task to achieve.
“It is like using a VMware server with multiple guest OSes,” explained Joanna Rutkowska, founder and CEO of Invisible Things Lab.
Qubes Supports Whonix (Anonymous Operating System)
Further, it supports all the operating system environment like:
- Microsoft Windows
- Linux distributions
- Whonix
Whonix is another security focused Linux-based operating system (Debian); it is capable of providing privacy, security and anonymity on the internet.
It enforces only Tor-based communication and allows Qubes users to connect to the Internet via a more secure anonymity-focused VM.
The team sitting at the ‘Invisible Things Project’ with the release of Qubes 3.0 are focussing on its successor, and they have already planned the maturing of the next version by the end of October.
Doesn’t sound so great does it?
Read More: Is This Security-Focused Linux Kernel Really UnHackable?
Doesn’t sound so great does it?
Read More: Is This Security-Focused Linux Kernel Really UnHackable?
Future Release: Qubes 3.1
- UEFI support
- Live USB Edition
- Management/pre-configuration stack: The Big Killer Feature of the upcoming 3.1 release, which will make it easy to provide out of the box configurations for things such as: out of the box Whonix/Tor, or Split GPG, or default USB sandboxing VM, which currently the user must do manually.
Finally, If We See, Why do we need Qubes?
Answer is: ‘Security Isolation.'
As Qubes allows various segments of your daily digital activities to run separately through virtualization. With virtualization comes security isolation, where each activity runs on an isolated different and unique virtual machine (VM).
Why "Security Isolation"?
Answer is: When on a single physical device, different instances (VMs) of varied activities are maintained, therefore this allows increased security- as on occurrence of an intrusion only the unique VM gets compromised without affecting the Host and other VMs.
Security isolation or software compartmentalization allows shielding from the cyber attacks, as when they hit you, your complete digital life goes topsy-turvy.
The architecture itself is set up to protect you as well, but Qubes OS is best for proactive users who don't mind doing a bit of work to set up a secure environment.
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.