Seagate, a popular vendor of hardware solutions, has a critical zero-day vulnerability in its Network Attached Storage (NAS) device software that possibly left thousands of its users vulnerable to hackers.
Seagate's Business Storage 2-Bay NAS product, found in home and business networks, is vulnerable to a zero-day Remote Code Execution vulnerability, currently affecting more than 2,500 publicly exposed devices on the Internet.
Seagate is one of the world’s largest vendor of hardware solutions, with products available worldwide. After Western Digital, Seagate ranked second and holds 41% of the market worldwide in supplying storage hardware products.
A security researcher, named OJ Reeves, discovered the zero-day remote code execution vulnerability on 7th October last year and, reported to the company totally in the white hat style. But even after 130 days of responsible disclosure, the zero-day bug remains unpatched till now.
In order to exploit the vulnerability, an attacker needs to be on the same network as the vulnerable device which gives the attacker root access of the vulnerable device, without the need of a valid login. Reeves also released a python exploit along with its Metasploit module version which is available on Github.
ORIGIN OF ZERO-DAY VULNERABILITY
Seagate's Business Storage 2-Bay NAS products come with a web-enabled management application that lets administrators to perform device configuration functions such as adding users, setting up access control, managing files, and more.
This web application is built with three core technologies, including PHP version 5.2.13, CodeIgniter version 2.1.0 and Lighttpd version 1.4.28, which are all out-dated versions.
- PHP version 5.2.13 is vulnerable (CVE-2006-7243) that allows user-controlled data to prematurely terminate file paths, allowing for full control over the file extension.
- CodeIgniter version prior to 2.2.0 is vulnerable (CVE-2014-8686) that allows an attacker to extract the encryption key and decrypt the content of the cookie. Once decrypted, attacker can modify the content of the cookie and re-encrypt it prior to submitting it back to the server.
The custom web application authenticate the login user based upon browser cookies, having three parameters:
- username: logged in user name
- is_admin: user is admin or not i.e. Yes or No
- language: chosen language (eg. en_US)
Researcher explained that there is no further validation of user credentials at server-end, once username cookie is established, which could be impersonated easily by an attacker.
Another parameter 'is_admin' can be manipulated to 'Yes' value that allows the attacker to self-elevate to administrative privileges in the web application itself.
"The fact that a static session encryption key is in use across all instances of the NAS means that once a user has a valid session cookie on one instance, they can apply that same cookie directly to another instance and acquire the same level of access. In short, once a user is logged in as admin on one instance, they’re effectively admin on every instance," Reeves explained in an advisory.
The language parameter can be manipulated for exploitation of a local file inclusion vulnerability. At last, the web application is being executed by an instance of Lighttpd which is running under the context of the root user.
When an attacker makes a request with the manipulated cookie, it results in arbitrary code execution as root user. Therefore, successful exploitation of this vulnerability could result in taking complete control of the vulnerable device as a root user.
VULNERABLE PRODUCTS
Two different network storage devices made by Seagate were tested and found to be vulnerable. The latest Seagate NAS firmware version listed below are affected by this zero-day vulnerability:
- Business Storage 2-Bay NAS version 2014.00319
- Business Storage 2-Bay NAS version 2013.60311
However, Reeves believes that all versions of Business Storage 2-Bay NAS product prior to 2014.00319 are affected by the same vulnerability.
METASPLOIT MODULE AVAILABLE
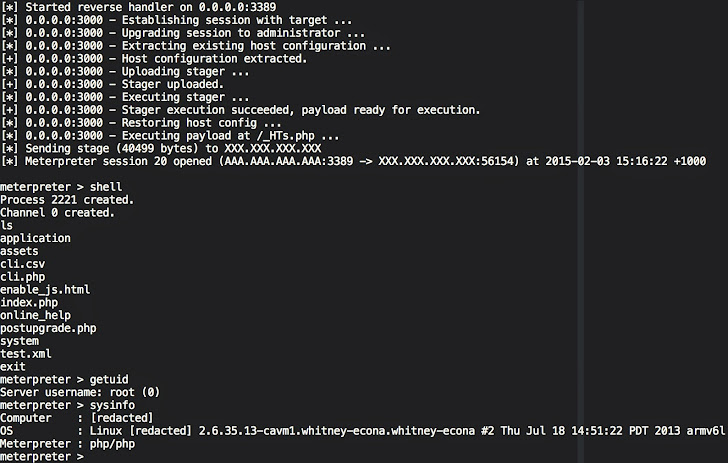
A Metasploit module and a Python script to exploit the vulnerability automatically is available on the Github. Each of these scripts are able to perform the following tasks:
- Connects to the vulnerable NAS device and extracts a ci_session cookie.
- Decrypts the cookie using the static encryption key and extracts the PHP hash.
- Modifies the serialized PHP hash so that the username is set to 'admin' and the is_admin field is set to 'yes'.
- Encrypts this updated PHP hash ready for further use as a ci_session cookie, which allows future requests to operate on the NAS as if they were an administrator.
- Performs a request to extract the host configuration, which includes the device's description.
- Modifies the host configuration so that the device description contains a small stager payload.
- Performs a request to update the host configuration with the new data so that the stager payload is written to /etc/devicedesc.
- Modifies the PHP hash again so that the language parameter contains the value ../../../../etc/devicedesc\x00.
- Encrypts this new PHP hash ready for future use as a ci_session cookie.
- Performs a request to the NAS using the cookie created in the previous step, which invokes the stager that was written to disk. This request posts a larger payload which is written to disk under the web server root.
- Performs another request which then resets the host configuration back to what it was prior to exploitation.
According to Reeves, there was no updated firmware version available for download that contains patches for the issues, even after contacting the company multiple times.
Users of Seagate's Business Storage NAS products and and other products using vulnerable firmware are recommended to ensure that their devices are not accessible via the public Internet and that the devices be located behind a firewall configured to allow only a trusted set of IP addresses to connect to the web interface.
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.