Attack surface management (ASM) and vulnerability management (VM) are often confused, and while they overlap, they’re not the same. The main difference between attack surface management and vulnerability management is in their scope: vulnerability management checks a list of known assets, while attack surface management assumes you have unknown assets and so begins with discovery. Let’s look at both in more detail.
What is vulnerability management?
Vulnerability management is, at the simplest level, the use of automated tools to identify, prioritize and report on security issues and vulnerabilities in your digital infrastructure.
Vulnerability management uses automated scanners to run regular, scheduled scans on assets within a known IP range to detect established and new vulnerabilities, so you can apply patches, remove vulnerabilities or mitigate any potential risks. These vulnerabilities tend to use a risk score or scale – such as CVSS – and risk calculations.
Vulnerability scanners often have many thousands of automated checks at their disposal, and by probing and gathering information about your systems, they can identify security gaps which could be used by attackers to steal sensitive information, gain unauthorized access to your systems, or disrupt your business. Armed with this knowledge, you can protect your organization and prevent potential attacks.
 |
| A screenshot of the Intruder vulnerability management platform, which is designed to perform thousands of security checks, identifying vulnerabilities in web apps, APIs, cloud systems, and beyond. |
What is the vulnerability management process?
- Performing a vulnerability scan
- Assessing your vulnerability risk
- Prioritizing and fixing vulnerabilities
- Monitoring continuously
What is attack surface management?
The main difference between vulnerability management and attack surface management is the scope. Attack surface management (ASM) includes asset discovery – helping you to find all your digital assets and services and then reducing or minimizing their exposure to prevent hackers from exploiting them.
With ASM, all known or unknown assets (on-premises, cloud, subsidiary, third-party, or partner environments) are detected from the attacker’s perspective from outside the organization. If you don’t know what you’ve got, how can you protect it?
Take the example of an admin interface like cPanel or a firewall administration page – these may be secure against all known current attacks today, but a vulnerability could be discovered tomorrow – when it becomes a significant risk. If you monitor and reduce your attack surface, regardless of vulnerabilities, you become harder to attack.
So, a significant part of attack surface management is reducing exposure to possible future vulnerabilities by removing unnecessary services and assets from the internet. But to do this, first you need to know what’s there.
What is the attack surface management process?
- Discover and map all your digital assets
- Ensure visibility and create a record of what exists
- Run a vulnerability scan to identify any weaknesses
- Automate so everyone who creates infrastructure can do so securely
- Continuously monitor as new infrastructure and services are spun up
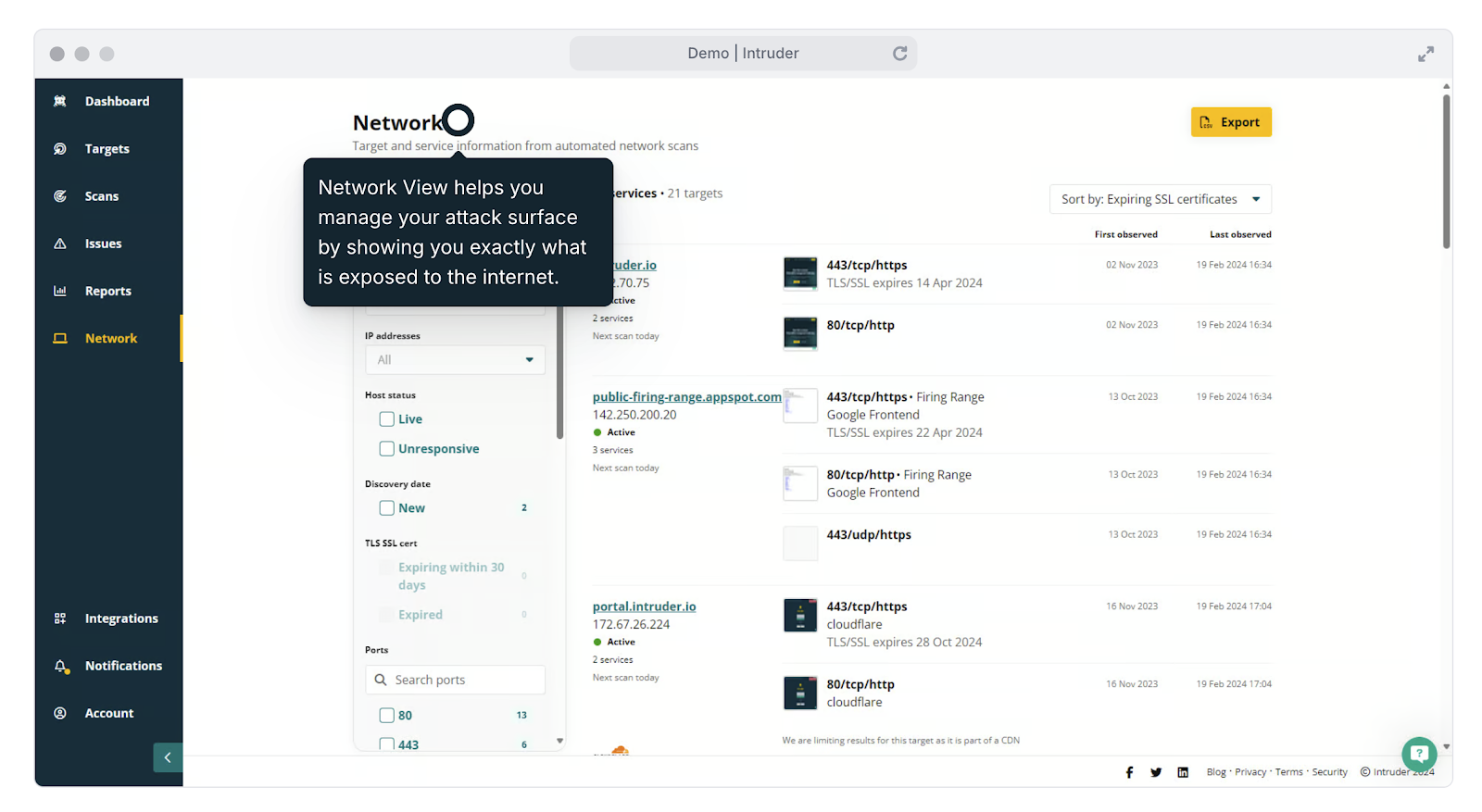 |
| Intruder’s attack surface management features help you to stay on top of changes in your environment, such as recently opened ports and services. |
How does attack surface management differ from vulnerability management?
Vulnerability management is the process of identifying and prioritizing vulnerabilities in your IT infrastructure and applications. Attack surface management goes a step further by identifying and analyzing your attack surface – all the devices, entry points and exposed services that an attacker could potentially use to gain access to your systems or data.
Can you combine Attack Surface Management and Vulnerability Management?
While ASM and VM may have different scopes and objectives, they’re not mutually exclusive. Used in combination, they create a much more holistic, robust and comprehensive cyber security posture. By identifying your assets and vulnerabilities, you can prioritize your security efforts and allocate resources more effectively – which will help you reduce the likelihood of a successful attack and any potential impact.
How Intruder can help with ASM and VM
Ultimately, you want to leave no stone unturned when it comes to cyber security. Modern VM and ASM solutions like Intruder can detect vulnerabilities affecting your organization. It gives you greater visibility and control over your attack surface, monitors network changes and SSL/TLS certificate expiry dates, helps you stay on top of your cloud infrastructure, and allows you to pay only for active targets. Why not see for yourself with a free 14-day trial?




























