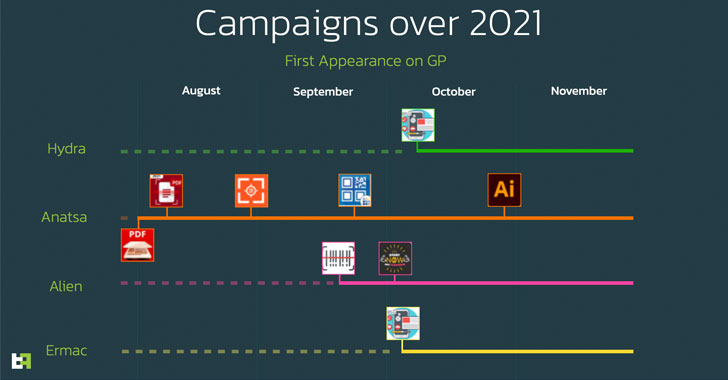
Four different Android banking trojans were spread via the official Google Play Store between August and November 2021, resulting in more than 300,000 infections through various dropper apps that posed as seemingly harmless utility apps to take full control of the infected devices.
Designed to deliver Anatsa (aka TeaBot), Alien, ERMAC, and Hydra, cybersecurity firm ThreatFabric said the malware campaigns are not only more refined, but also engineered to have a small malicious footprint, effectively ensuring that the payloads are installed only on smartphones devices from specific regions and preventing the malware from being downloaded during the publishing process.
Once installed, these banking trojans can surreptitiously siphon user passwords and SMS-based two-factor authentication codes, keystrokes, screenshots, and even deplete users' bank accounts without their knowledge by using a tool called Automatic Transfer System (ATSs). The apps have since been removed from the Play Store.
The list of malicious dropper apps is below -
- Two Factor Authenticator (com.flowdivison)
- Protection Guard (com.protectionguard.app)
- QR CreatorScanner (com.ready.qrscanner.mix)
- Master Scanner Live (com.multifuction.combine.qr)
- QR Scanner 2021 (com.qr.code.generate)
- QR Scanner (com.qr.barqr.scangen)
- PDF Document Scanner - Scan to PDF (com.xaviermuches.docscannerpro2)
- PDF Document Scanner Free (com.doscanner.mobile)
- CryptoTracker (cryptolistapp.app.com.cryptotracker)
- Gym and Fitness Trainer (com.gym.trainer.jeux)
While Google earlier this month instituted limitations to restrict the use of accessibility permissions that allow malicious apps to capture sensitive information from Android devices, operators of such apps are increasingly refining their tactics by other means even when forced to choose the more traditional way of installing apps through the app marketplace.
Chief among the techniques is a technique called versioning, wherein clean versions of the apps are first uploaded, and malicious functionalities are incrementally introduced in the form of subsequent app updates. Another tactic involves designing look-alike command-and-control (C2) websites that match the theme of the dropper app so as to slip past conventional detection methods.
ThreatFabric discovered six Anatsa droppers on the Play Store since June 2021, with the apps programmed to download an "update" followed by prompting users to grant it Accessibility Service privileges and permissions to install apps from unknown third-party sources.
Brunhilda, a threat actor which was discovered distributing a remote access trojan named Vultur in July 2021, leveraged trojanized apps masquerading as QR code creator apps to drop Hydra and ERMAC malware aimed at users in the U.S., a market previously not targeted by the two malware families.
Lastly, a fitness training dropper app with over 10,000 installations — dubbed GymDrop — was found delivering the Alien banking trojan payload by masking it as a "new package of workout exercises," even as its purportedly legitimate developer website doubled up as the C2 server to fetch the configuration required to download the malware.
"To make themselves even more difficult to detect, the actors behind these dropper apps only manually activate the installation of the banking trojan on an infected device in case they desire more victims in a specific region of the world," the researchers said. "This makes automated detection a much harder strategy to adopt by any organization."