Israeli organizations were targeted as part of two different campaigns orchestrated by the Iranian nation-state actor known as OilRig in 2021 and 2022.
The campaigns, dubbed Outer Space and Juicy Mix, entailed the use of two previously undocumented first-stage backdoors called Solar and Mango, which were deployed to collect sensitive information from major browsers and the Windows Credential Manager.
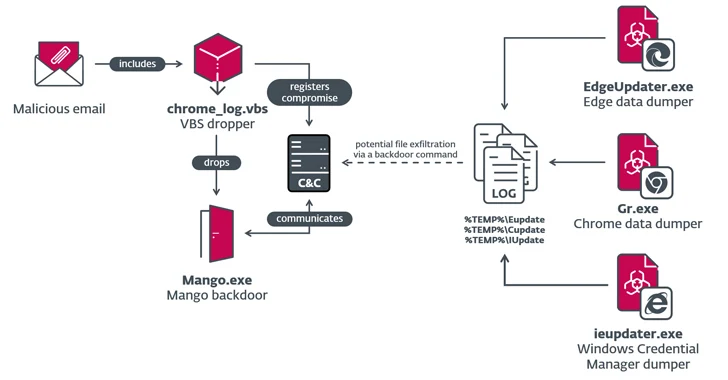
"Both backdoors were deployed by VBS droppers, presumably spread via spear-phishing emails," ESET security researcher Zuzana Hromcová said in a Thursday analysis.
OilRig (aka APT34, Cobalt Gypsy, Hazel Sandstorm, and Helix Kitten) is the name assigned to an intrusion set affiliated with Iran's Ministry of Intelligence and Security (MOIS). Active since 2014, the threat actor has used a wide range of tools at its disposal to carry out information theft.
Earlier this February, Trend Micro discovered OilRig's use of a simple backdoor to steal users' credentials, highlighting its "flexibility to write new malware based on researched customer environments and levels of access."
The group has also been observed delivering an updated version of SideTwist as part of a phishing attack likely targeting U.S. businesses.
That said, the use of Mango malware was previously highlighted by both ESET and Microsoft in May 2023, with the latter attributing it to an emerging activity cluster it tracks under the name Storm-0133.
Storm-0133, also associated with MOIS, exclusively targets Israeli local government agencies and companies serving the defense, lodging, and healthcare sectors, the Windows maker said.
The latest findings from the Slovak cybersecurity firm establish the group's continued focus on Israel, using spear-phishing lures to trick potential targets into installing the malware via booby-trapped attachments.
In the Outer Space campaign observed in 2021, OilRig compromised an Israeli human resources site and subsequently used it as a command-and-control (C2) server for Solar, a basic C#/.NET backdoor capable of downloading and executing files and gathering information.
Solar also acts as a vehicle to deploy a downloader named SampleCheck5000 (or SC5k), which uses the Office Exchange Web Services (EWS) API to download additional tools for execution, as well as a utility to exfiltrate data from the Chrome web browser referred to as MKG.
"Once SC5k logs into the remote Exchange server, it retrieves all the emails in the Drafts directory, sorts them by most recent, keeping only the drafts that have attachments," Hromcová said.
"It then iterates over every draft message with an attachment, looking for JSON attachments that contain "data" in the body. It extracts the value from the key data in the JSON file, base64 decodes and decrypts the value, and calls cmd.exe to execute the resulting command line string."
The results of the command execution are staged and sent back to the operators via a new email message on the Exchange server and saving it as a draft.
The Juicy Mix campaign of 2022 involved the use of Mango, an improved version of Solar incorporating additional capabilities and obfuscation methods. For C2 purposes, the threat actor compromised a legitimate Israeli job portal website.
"OilRig continues to innovate and create new implants with backdoor-like capabilities while finding new ways to execute commands on remote systems," Hromcová said.
"The group deploys a set of custom post-compromise tools that are used to collect credentials, cookies, and browsing history from major browsers and from the Windows Credential Manager."