A variant of the infamous Dridex banking malware has set its sights on Apple's macOS operating system using a previously undocumented infection method, according to latest research.
It has "adopted a new technique to deliver documents embedded with malicious macros to users without having to pretend to be invoices or other business-related files," Trend Micro researcher Armando Nathaniel Pedragoza said in a technical report.
Dridex, also called Bugat and Cridex, is an information stealer that's known to harvest sensitive data from infected machines and deliver and execute malicious modules. It's attributed to an e-crime group known as Evil Corp (aka Indrik Spider).
The malware is also considered to be a successor of Gameover Zeus, itself a follow-up to another banking trojan called Zeus. Previous Dridex campaigns targeting Windows have leveraged macro-enabled Microsoft Excel documents sent via phishing emails to deploy the payload.
A law enforcement operation orchestrated by Europe and the U.S. disrupted the botnet in October 2015 and a Moldovan national named Andrey Ghinkul was arrested for his role as an administrator of the operation. In December 2018, Ghinkul was sentenced to time served by a U.S. federal court following his extradition in February 2016.
Subsequently in December 2019, the U.S. Treasury Department imposed sanctions against Evil Corp and announced a $5 million bounty against two key members Maksim Yakubets and Igor Turashev. Despite these efforts, Dridex has continued to evolve, proving to be a resilient threat.
Trend Micro's analysis of the Dridex samples involves a Mach-O executable file, the earliest of which was submitted to VirusTotal in April 2019. Since then, 67 more artifacts have been detected in the wild, some as recent as December 2022.
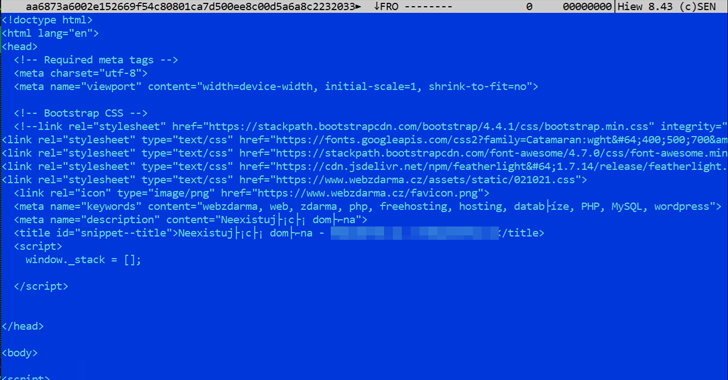
The artifact, for its part, contains a malicious embedded document – first detected way back in 2015 – that incorporates an Auto-Open macro that's automatically run upon opening a Word document.
Furthermore, the Mach-O executable is designed to search and overwrite all ".doc" files in the current user directory (~/User/{user name}) with the malicious macro code copied from the embedded document in the form of a hexadecimal dump.
"While the macro feature in Microsoft Word is disabled by default, the malware will overwrite all the document files for the current user, including the clean files," Pedragoza explained. "This makes it more difficult for the user to determine whether the file is malicious since it doesn't come from an external source."
The macros included in the overwritten document are engineered to contact a remote server to retrieve additional files, which includes a Windows executable file that will not run in macOS, indicating that the attack chain might be a work in progress. The binary, in turn, attempts to download the Dridex loader onto the compromised machine.
While documents containing booby-trapped macros are typically delivered via social engineering attacks, the findings once again show that Microsoft's decision to block macros by default has prompted threat actors to refine their tactics and find more efficient methods of entry.
"Currently, the impact on macOS users for this Dridex variant is minimized since the payload is an .EXE file (and therefore not compatible with macOS environments)," Trend Micro said. "However, it still overwrites document files which are now the carriers of Dridex's malicious macros."