LinkedIn's iOS application is prone to a vulnerability that may permit remote attackers to execute arbitrary code.
Security Researcher Zouheir Abdallah has disclosed HTML parsing vulnerability in LinkedIn iOS an app, that can be used to phish for credentials or be escalated into a full blown attack.
LinkedIn's vulnerability occurs when the messaging feature of LinkedIn's mobile app parses invalid HTML and an attacker can exploit this vulnerability remotely from his/her account, which could have serious impact on LinkedIn's users.
He created Proof of concept of the flaw and submitted it to the LinkedIn Security team in September 2013. Later in October 2013, the vulnerable application was patched.
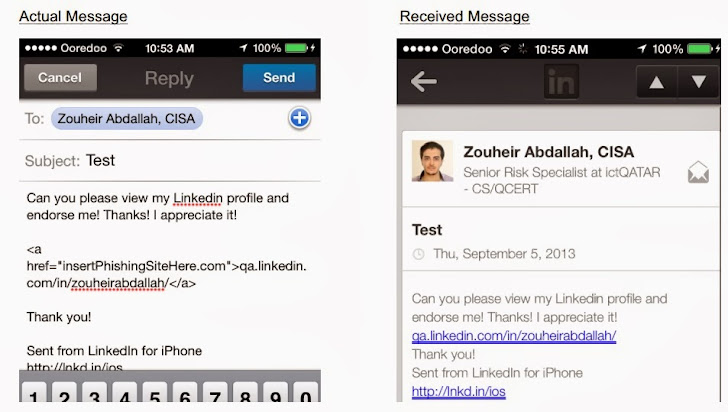
One of the possible attack vector is that, using this vulnerability attacker can easily phish LinkedIn user on iOS app. As shown in the screenshot, POC message says:
Hey, Can you please view my LinkedIn profile and endorse me! Thanks! I appreciate it!
The iOS app will display the url without the hyperlink embedded in the HTML a href , and the receiver of the message will not even know that he is being redirected to a malicious site.
The phishing site can be a replica of LinkedIn and tricks the victim into giving out his username and password.
This attack can also be used against LinkedIn users by claiming that, they have to re-authenticate to view some article on LinkedIn. The Same attack could also work on different devices such as Android and Blackberry, but he couldn’t test as he didn’t have other handsets at hand.
LinkedIn doesn't have a Bug Bounty program neither a Hall of Fame, nevertheless he received a symbolic token of a Shirt, Mug, and a thank you note from LinkedIn's security team.
Zouheir is known for reporting a serious vulnerability in DropBox's 2 Factor Authentication back in July 2013.
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.