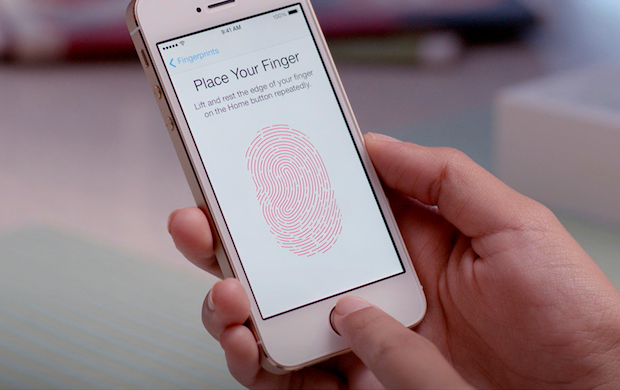
Apple has marketed TouchID both as a convenience and as a security feature. “Your fingerprint is one of the best passwords in the world,” says an Apple promotional video.
A European hacker group has announced a simple, replicable method for spoofing Apple’s TouchID fingerprint authentication system.
The Apple TouchID it the technology developed by Apple to replace passcode on its mobile and help protect users' devices, it is based on a sensor placed under the home button and it is designed to substitute the four-digit passcode to unlock the handset and authorize iTunes Store purchases.
A European hacker group has announced a simple, replicable method for spoofing Apple’s TouchID fingerprint authentication system.
The Apple TouchID it the technology developed by Apple to replace passcode on its mobile and help protect users' devices, it is based on a sensor placed under the home button and it is designed to substitute the four-digit passcode to unlock the handset and authorize iTunes Store purchases.
But is it really so? Hackers members of the Chaos Computer Club claim to have defeated Apple TouchID fingerprint sensor for the iPhone 5S, just after the start of its sale to the public. "Fingerprints should not be used to secure anything. You leave them everywhere, and it is far too easy to make fake fingers out of lifted prints," a hacker named Starbug was quoted as saying on the CCC's site.
They have successfully bypassed the biometric security on the Apple's Touch ID fingerprint sensor by using materials that can be found in almost every household, it seems that they made it by photographing an iPhone user's fingerprint from a glass surface and using that captured image to verify the user's login credentials.
It warned users to consider whether they want to use a security system that you cannot change unless you change your hands. "In reality, Apple's sensor has just a higher resolution compared to the sensors so far. So we only needed to ramp up the resolution of our fake", post said.
Although CCC did not demonstrate this, several videos have surfaced demonstrated the ease at which the biometric security found on Apple's iPhone 5S can be bypassed.
First, the fingerprint of the enrolled user is photographed with 2400 dpi resolution. The resulting image is then cleaned up, inverted and laser printed with 1200 dpi onto transparent sheet with a thick toner setting. Finally, pink latex milk or white woodglue is smeared into the pattern created by the toner onto the transparent sheet. After it cures, the thin latex sheet is lifted from the sheet, breathed on to make it a tiny bit moist and then placed onto the sensor to unlock the phone. This process has been used with minor refinements and variations against the vast majority of fingerprint sensors on the market.
"We hope that this finally puts to rest the illusions people have about fingerprint biometrics," "It is plain stupid to use something that you can´t change and that you leave everywhere every day as a security token." added CCC spokesperson Frank Rieger.
The hack is embarrassing, in recent days a series of bugs and security issues were found on the last version of the popular Apple OS, iOS 7, in particular the lockscreen features is affected by serious flaws.
"The public should no longer be fooled by the biometrics industry with false security claims. Biometrics is fundamentally a technology designed for oppression and control, not for securing everyday device access." hacker said.
"We hope that this finally puts to rest the illusions people have about fingerprint biometrics," "It is plain stupid to use something that you can´t change and that you leave everywhere every day as a security token." added CCC spokesperson Frank Rieger.
The hack is embarrassing, in recent days a series of bugs and security issues were found on the last version of the popular Apple OS, iOS 7, in particular the lockscreen features is affected by serious flaws.
"The public should no longer be fooled by the biometrics industry with false security claims. Biometrics is fundamentally a technology designed for oppression and control, not for securing everyday device access." hacker said.
These are the exact same steps that the CCC published in 2004 on its web site and the same process that can be used, with minor tweaks, to trick the vast majority of fingerprint sensors on the market.
At this point the only question to be clarified is if the hackers will claim to the bounty of more than $16,000 in cash offered to the first person to hack the Apple TouchID fingerprint sensor.
IsTouchIDhackedyet.com is the brainchild of Nick DePetrillo, an independent security researcher whose last major public research was 2010's Carmen San Diego Project, it announced on its Web site that it was waiting for the group to upload video of the hack as proof of the hack.
Rewards include also a patent application from CipherLaw for the hack process, some Scotch, and a book of erotica.
Lesson learned ... nothing is secure!
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.