Indian Security Research Atul Alex presented his surprise paper at the International Malware Conference, MalCon on what can be termed as the onset of next generation of hardware based malware that can target mobile devices irrespective of Platforms.
Typically, one of the largest challenges for malware coders are to target multiple platforms. A malware for Android will not work in Windows phone, Symbian or Apple iOS, which come in way of malware coders. Also, devices such as iPhone are extremely secure and there is little that can be extracted from a locked / secure iPhone, unless they are jailbroken.
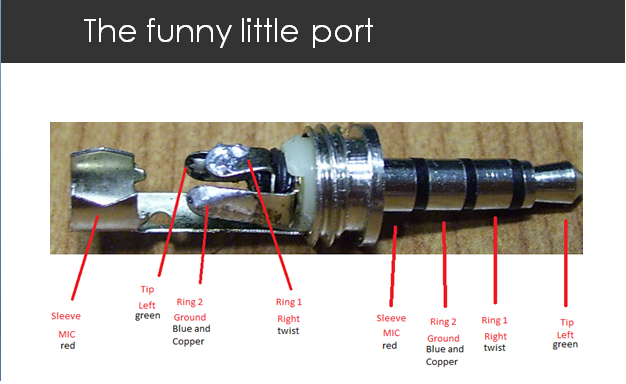
Atul Alex's research abuses voice dialing feature which is enabled by default on all mobile platforms - and combines a bugged headset with a micro controller and code to steal private data. The bugged headset can also dial a pre-defined number by detecting if the device is in use or not and turn the phone into a spy device. Further, it can steal contacts from all devices - Blackberry, iphone, Symbian, Windows and Android, without putting a malware inside the mobile phone.
The bugged headset can in fact mimic voice commands and send it to the device discretely - and Alex mentioned that advanced software like SIRI can infact aid hackers in future in sending unauthorized text messages as well as extract personal data and device information.
Any mobile device running Google Android, Microsoft Windows Phone, Apple IOS 5, or Blackberry OS provides voice command capabilities. Some of the other possible things include knowing call duration and even record incoming and outgoing calls of users. And all this is possible just by plugging a bugged headset into the Audio jack.
This has long term future implications and provides a grim future with electronics warfare. Malwares can now target people across all platforms, irrespective of 0-days in browsers, OS etc present or not.. and the last thing one would suspect is a gifted headset or speaker dock for your device.
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.