Morto Worm spreading via Remote Desktop Protocol
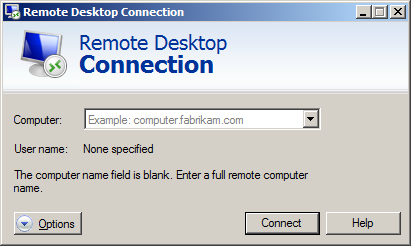
Organizations large and small often make use of Remote Desktop or Terminal Services to remotely connect to Windows computers over the Internet and internally. These tools use Microsoft’s RDP protocol to allow the user to operate the remote system almost as if sitting in front of it. Such capabilities are helpful for not only legitimate users, but also for attackers.
F-Secure is reporting that the worm is behind a spike in traffic on Port 3389/TCP. Once it’s entered a network, the worm starts scanning for machines that have RDP enabled. Vulnerable machines get Morto copied to their local drives as a DLL, a.dll, which creates other files detailed in the F-Secure post.
Organizations large and small often make use of Remote Desktop or Terminal Services to remotely connect to Windows computers over the Internet and internally. These tools use Microsoft’s RDP protocol to allow the user to operate the remote system almost as if sitting in front of it. Such capabilities are helpful for not only legitimate users, but also for attackers.
F-Secure is reporting that the worm is behind a spike in traffic on Port 3389/TCP. Once it’s entered a network, the worm starts scanning for machines that have RDP enabled. Vulnerable machines get Morto copied to their local drives as a DLL, a.dll, which creates other files detailed in the F-Secure post.
The emergence of this worm correlates with the increased volumes of TCP port 3389 traffic, reported by SANS Internet Storm Center a few days prior to the F-Secure report:
The propagation approach employed by “Morto” is often used by penetration testers and human attackers alike: access the remote host by brute-forcing the password. One free tool that can automate this process is TSGrinder.F-Secure also fingers jaifr.com and qfsl.net as servers being used to remotely control the Morto worm
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.