More details have emerged about the operators behind the first-known phishing campaign specifically aimed at the Python Package Index (PyPI), the official third-party software repository for the programming language.
Connecting it to a threat actor tracked as JuiceLedger, cybersecurity firm SentinelOne, along with Checkmarx, described the group as a relatively new entity that surfaced in early 2022.
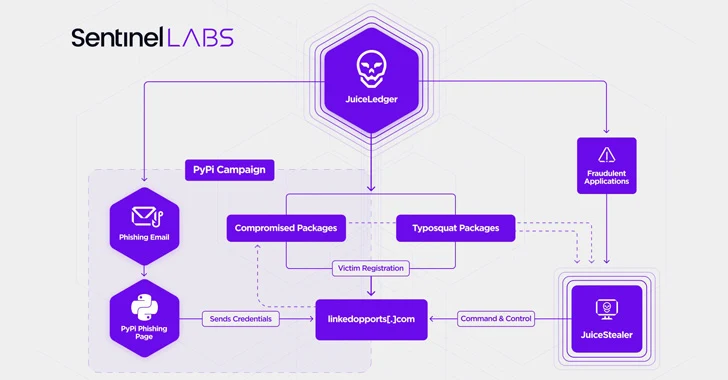
Initial "low-key" campaigns are said to have involved the use of rogue Python installer applications to deliver a .NET-based malware called JuiceStealer that's engineered to siphon passwords and other sensitive data from victims' web browsers.
The attacks received a significant facelift last month when the JuiceLedger actors targeted PyPi package contributors in a phishing campaign, resulting in the compromise of three packages with malware.
"The supply chain attack on PyPI package contributors appears to be an escalation of a campaign begun earlier in the year which initially targeted potential victims through fake cryptocurrency trading applications," SentinelOne researcher Amitai Ben Shushan Ehrlich said in a report.
The goal is presumably to infect a wider audience with the infostealer through a mix of trojanized and typosquat packages, the cybersecurity firm added.
The development adds to growing concerns surrounding the security of the open source ecosystem, prompting Google to take steps to announce monetary rewards for finding flaws in its projects available in the public domain.
With account takeover attacks becoming a popular infection vector for attackers looking to poison software supply chains, PyPI has begun imposing a mandatory two-factor authentication (2FA) requirement for projects deemed "critical."
"JuiceLedger appears to have evolved very quickly from opportunistic, small-scale infections only a few months ago to conducting a supply chain attack on a major software distributor," SentinelOne said.
"The escalation in complexity in the attack on PyPI contributors, involving a targeted phishing campaign, hundreds of typosquatted packages and account takeovers of trusted developers, indicates that the threat actor has time and resources at their disposal."