The notorious Emotet malware is staging a comeback of sorts nearly 10 months after a coordinated law enforcement operation dismantled its command-and-control infrastructure in late January 2021.
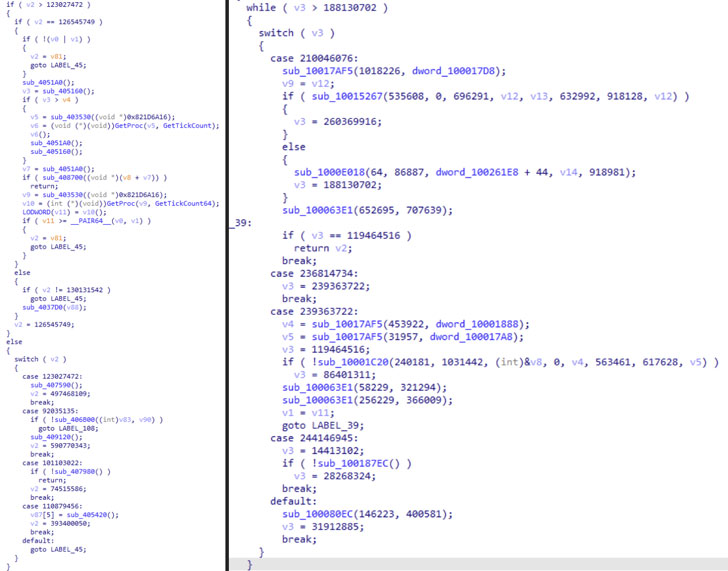
According to a new report from security researcher Luca Ebach, the infamous TrickBot malware is being used as an entry point to distribute what appears to be a new version of Emotet on systems previously infected by the former. The latest variant takes the form of a DLL file, with the first occurrence of the deployment being detected on November 14.
Europol dubbed Emotet as the "world's most dangerous malware" for its ability to act as a "door opener" for threat actors to obtain unauthorized access, becoming a precursor to many critical data theft and ransomware attacks. Interestingly, the loader operation enabled other malware families such as Trickbot, QakBot, and Ryuk to enter a machine.
The resurfacing is also significant not least because it follows concerted efforts on the part of the law enforcement to automatically uninstall the malware en masse from the compromised computers in April.
As of writing, malware tracking research project Abuse.ch's Feodo Tracker shows nine Emotet command-and-control servers that are currently online, implying that the operators are trying to revive the botnet up and get it running again.
Samples of the new Emotet loader can be accessed here. To prevent devices from being co-opted into the newly active Emotet botnet, network administrators are strongly recommended to block all the relevant IP addresses.
Update: In a matter of less than 24 hours, the Emotet botnet has expanded its botnet command-and-control (C2) infrastructure from 9 active C2 servers to 14 active C2 servers. "It seems to be very clear that Emotet is firing up its activity," Abuse.ch said in a tweet.
The increase in Emotet activity has also been accompanied by a surge in malspam campaigns, with select infection chains dropping the loader directly using macro-enabled Word and Excel documents attached to stolen email threads without relying on TrickBot.
"[Emotet is] back and retooled. Code and infrastructure has had updates, it is better secured now. It must be somebody/somebodies with access to original source code," security researcher Kevin Beaumont tweeted.