Cybersecurity researchers on Wednesday took the wraps off a "simple yet remarkable" malware loader for malicious Windows binaries targeting Central Europe, North America and the Middle East.
Codenamed "Wslink" by ESET, this previously undocumented malware stands apart from the rest in that it runs as a server and executes received modules in memory. There are no specifics available on the initial compromise vector and there are no code or operational overlaps that tie this tool to a known threat actor group.
The Slovak cybersecurity firm noted that it has seen only a handful of detections in the past two years, suggesting that it could be used in highly-targeted cyber infiltrations.
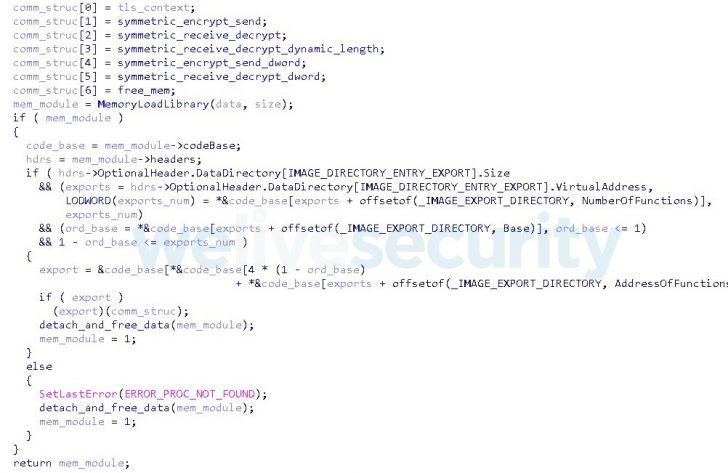
Wslink is designed to run as a service and can accept encrypted portal executable (PE) files from a specific IP address, which is then decrypted and loaded into memory prior to the execution. To achieve this, the client (i.e., the victim) and the server perform a handshake that involves the exchange of cryptographic keys necessary to encrypt the modules using AES.
"Interestingly, the modules reuse the loader's functions for communication, keys and sockets; hence they do not have to initiate new outbound connections," ESET researcher Vladislav Hrčka said. "Wslink additionally features a well-developed cryptographic protocol to protect the exchanged data."
The findings come as researchers from Zscaler and Cisco Talos disclosed yet another malware loader called SQUIRRELWAFFLE that's distributed via spam email campaigns to deploy Qakbot and Cobalt Strike on compromised systems.