Ping.fm vulnerable to Clickjacking (Video Demonstration)
This is based on a technique known as clickjacking ( or UI Redressing ) where an attacker could perform actions on the behalf of user by tricking the user to click on a button or perform some other action.
This vulnerability was earlier seen in Twitter where it allows the status to be loaded through the GET method, and an attacker could frame the twitter webpage and trick the user to click on the tweet button, with the user thinking that its a part of the attacker's webpage.
This can be disabled by setting the X-FRAME-ORIGIN method to SAME ORIGIN or DENYING the use of webpage inside a frame which have been adopted by google, facebook and many other famous websites.
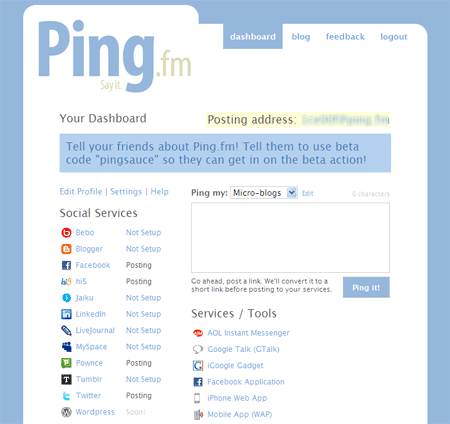
Two Indian Hackers Aditya Gupta(@adi1391) and Subho Halder (@sunnyrockzzs) have discovered Clickjacking vulnerability in one of the famous website "Ping.FM". Clickjacking is a malicious technique of tricking Web users into revealing confidential information or taking control of their computer while clicking on seemingly innocuous web pages.
This is based on a technique known as clickjacking ( or UI Redressing ) where an attacker could perform actions on the behalf of user by tricking the user to click on a button or perform some other action.
This vulnerability was earlier seen in Twitter where it allows the status to be loaded through the GET method, and an attacker could frame the twitter webpage and trick the user to click on the tweet button, with the user thinking that its a part of the attacker's webpage.
This can be disabled by setting the X-FRAME-ORIGIN method to SAME ORIGIN or DENYING the use of webpage inside a frame which have been adopted by google, facebook and many other famous websites.
Ping.fm is a online service which allows the user to connect to many social networks at once. However an attacker could use a technique known as Clickjacking to silently update the user's social networking status at Twitter, Facebook and all other connected accounts.In this technique, the user is tricked into clicking on a button on a webpage designed by the attacker,which silently updates the status of the user on the social netowrks status taking advantage of thePing.fm API and clickjacking technique.
Video Demonstration POC :
Video Demonstration POC :
Found this article interesting? Follow us on Google News, Twitter and LinkedIn to read more exclusive content we post.