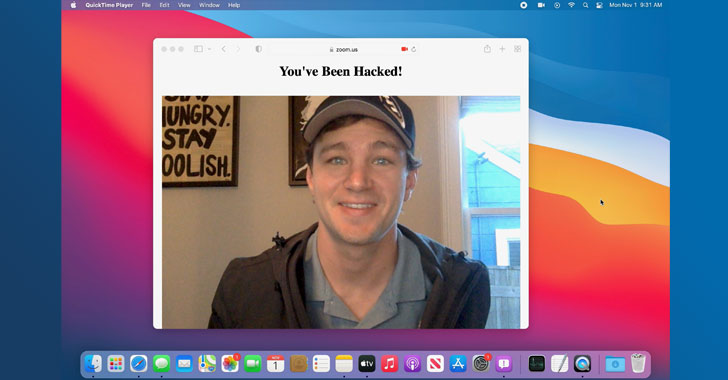
Apple last year fixed a new set of macOS vulnerabilities that exposed Safari browser to attack, potentially allowing malicious actors to access users' online accounts, microphone, and webcam.
Security researcher Ryan Pickren, who discovered and reported the bugs to the iPhone maker, was compensated with a $100,500 bug bounty, underscoring the severity of the issues.
By exploiting a chain of security issues with iCloud Sharing and Safari 15, it enables the attacker to hijack the multimedia permission and gain "full access to every website ever visited by the victim" in Safari, including Gmail, iCloud, Facebook, and PayPal accounts.
The issues specifically concern ShareBear, an iCloud file-sharing mechanism that prompts users upon attempting to open a shared document for the first time. Taking advantage of the fact that users are never displayed the prompt again once they accept to open the file, Pickren found that it's possible to alter the file's content to anything by anyone with access to the file.
"ShareBear will then download and update the file on the victim's machine without any user interaction or notification," Pickren explained in a technical write-up. "In essence, the victim has given the attacker permission to plant a polymorphic file onto their machine and the permission to remotely launch it at any moment."
In other words, an image file with a .PNG format could have its entire content and extension changed to an executable binary ("evil.dmg") after the user has agreed to open it. The binary can then be launched, triggering an exploit chain that leverages additional flaws discovered in Safari to take over the machine's mic or webcam, or even steal local files —
- CVE-2021-30861 – A logic issue in WebKit that could allow a malicious application to bypass Gatekeeper checks
- CVE-2021-30975 – An issue in Script Editor that could allow a malicious OSAX scripting addition to bypass Gatekeeper checks and circumvent sandbox restrictions
This is the second time Pickren has disclosed flaws in iOS and macOS that, if successfully exploited, could be abused to access the camera in an unauthorized manner upon visiting a specially crafted website.
"This project was an interesting exploration of how a design flaw in one application can enable a variety of other, unrelated, bugs to become more dangerous," Pickren said. "It was also a great example of how even with macOS Gatekeeper enabled, an attacker can still achieve a lot of mischief by tricking approved apps into doing malicious things."