Interpol on Monday announced the arrest of three suspected global scammers in Nigeria for using remote access trojans (RATs) such as Agent Tesla to facilitate malware-enabled cyber fraud.
"The men are thought to have used the RAT to reroute financial transactions, stealing confidential online connection details from corporate organizations, including oil and gas companies in South East Asia, the Middle East and North Africa," the International Criminal Police Organization said in a statement.
One of the scammers in question, named Hendrix Omorume, has been charged and convicted of three counts of financial fraud and has been sentenced to a 12-month prison term. The two other suspects are still on trial.
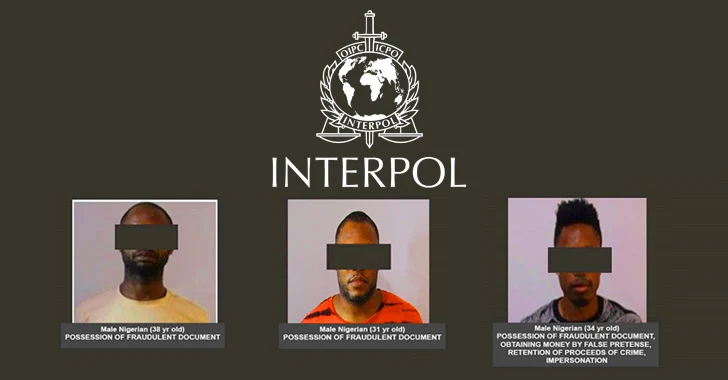
The three Nigerian individuals, who are aged between 31 and 38, have been apprehended for being in possession of fake documents such as fraudulent invoices and forged official letters.
The law enforcement said that the suspects systematically used Agent Tesla to breach business computers and divert financial transactions to bank accounts under their control.
A .NET-based advanced malware that first appeared in 2014, Agent Tesla primarily gets delivered through phishing emails and has capabilities such as keylogging, screen capture, form-grabbing, credential stealing, and exfiltrating other sensitive information.
The arrests follow a sting operation conducted simultaneously in two different locations in the Nigerian cities of Lagos and Benin City, with private sector intelligence provided by cybersecurity company Trend Micro.
The operation is also part of a global law enforcement operation codenamed "Killer Bee" involving Interpol and authorities from 11 different countries across Southeast Asia, including Brunei, Cambodia, Indonesia, Laos, Malaysia, Myanmar, Philippines, Singapore, Thailand, and Vietnam.
The development also comes close on the heels of the alleged leader of the SilverTerrier BEC cybercrime gang in a separate operation dubbed Delilah. It was preceded by two related operations called Falcon I and Falcon II in 2020 and 2021.