The malware known as DirtyMoe has gained new worm-like propagation capabilities that allow it to expand its reach without requiring any user interaction, the latest research has found.
"The worming module targets older well-known vulnerabilities, e.g., EternalBlue and Hot Potato Windows privilege escalation," Avast researcher Martin Chlumecký said in a report published Wednesday.
"One worm module can generate and attack hundreds of thousands of private and public IP addresses per day; many victims are at risk since many machines still use unpatched systems or weak passwords."
Active since 2016, the DirtyMoe botnet is used for carrying out cryptojacking and distributed denial-of-service (DDoS) attacks, and is deployed by means of external exploit kits like Purple Fox or injected installers of Telegram Messenger.
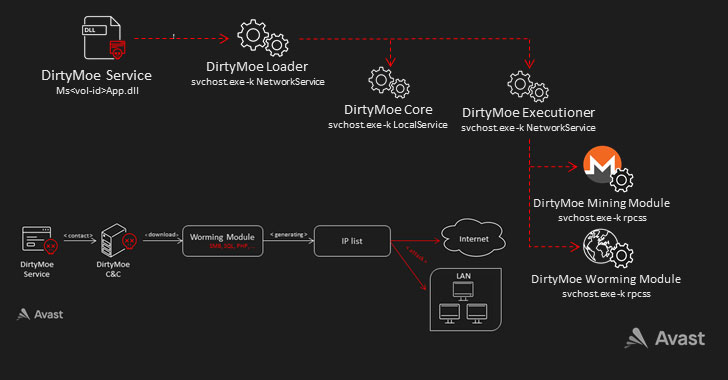
Also employed as part of the attack sequence is a DirtyMoe service that triggers the launch of two additional processes, namely the Core and the Executioner, which is used to load the modules for Monero mining and to spread the malware in a worm-like manner.
The worming modules attack victim machines by using several vulnerabilities to install the malware, with each module targeting a specific flaw based on information gathered post reconnaissance –
- CVE-2019-9082: ThinkPHP – Multiple PHP Injection RCEs
- CVE-2019-2725: Oracle Weblogic Server – 'AsyncResponseService' Deserialization RCE
- CVE-2019-1458: WizardOpium Local Privilege Escalation
- CVE-2018-0147: Deserialization Vulnerability
- CVE-2017-0144: EternalBlue SMB Remote Code Execution (MS17-010)
- MS15-076: RCE Allow Elevation of Privilege (Hot Potato Windows Privilege Escalation)
- Dictionary attacks aimed at MS SQL Servers, SMB, and Windows Management Instrumentation (WMI) services with weak passwords
"The main goal of the worming module is to achieve RCE under administrator privileges and install a new DirtyMoe instance," Chlumecký explained, adding one of the component's core functions is to generate a list of IP addresses to attack based on the geological location of the module.
Furthermore, another in-development worming module was found to contain exploits targeting PHP, Java Deserialization, and Oracle Weblogic Servers, implying that the attackers are looking to broaden the scope of the infections.
"Worming target IPs are generated utilizing the cleverly designed algorithm that evenly generates IP addresses across the world and in relation to the geological location of the worming module," Chlumecký said. "Moreover, the module targets local/home networks. Because of this, public IPs and even private networks behind firewalls are at risk."