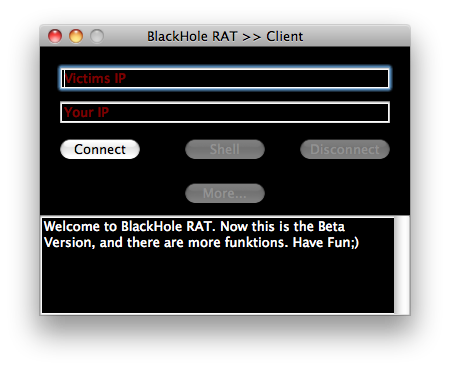
'BlackHole' is the latest remote administration tool (RAT) and is available both in Windows and Mac.
Hacktool such RAT employs client-server program that communicates to its victim's machine through its trojan server. The server application is installed on the victim while the client application is on the managing side.
The version suggest that 'BlackHole' is currently in its early stage. However, the author seems to start showcasing the following functionalities:
- Remote execution of shell commands.
- Opens webpage using user's default browser.
- Sends a message which is displayed on the victims screen.
- Creates a text file.
- It is capable to perform shutdown, restart and sleep operation.
- It is capable to request for admin privileges.
Here is an excerpt from the default text that is displayed in the full screen window with the reboot button:
"I am a Trojan Horse, so i have infected your Mac Computer. I know, most people think Macs can't be infected, but look, you ARE Infected!I have full controll over your Computer and i can do everything I want, and you can do nothing to prevent it.So, Im a very new Virus, under Development, so there will be much more functions when im finished."
Be wary of possible backdoor infection. Report suspicious application, especially if it is communicating to unknown or unfamiliar remote server.
Note: While checking the client-server capability, I just thought that it would be useful to capture a video for reference. (recommended screen 720pHD)